
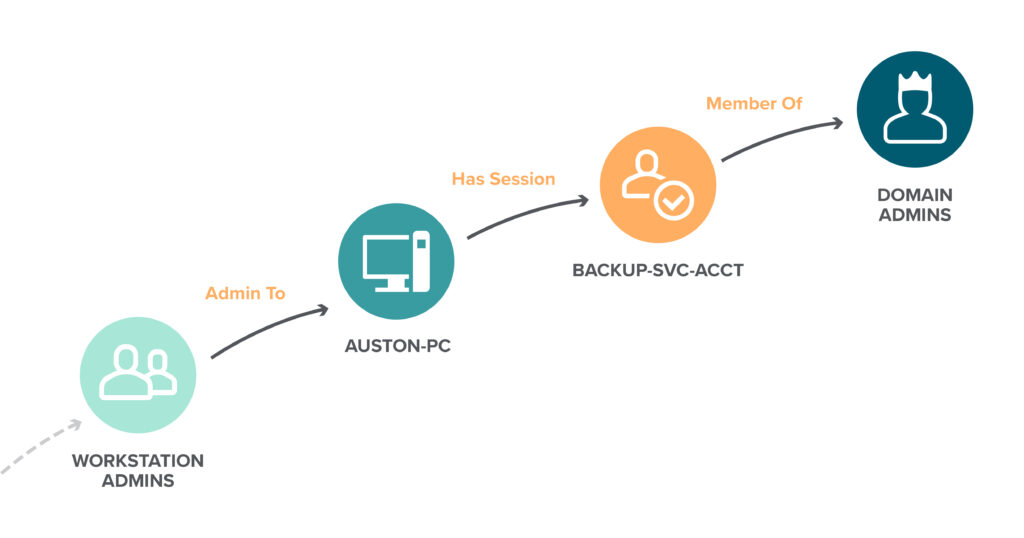
Chaining together Active Directory attack techniques to give your organization the edge against attackers | XM Cyber
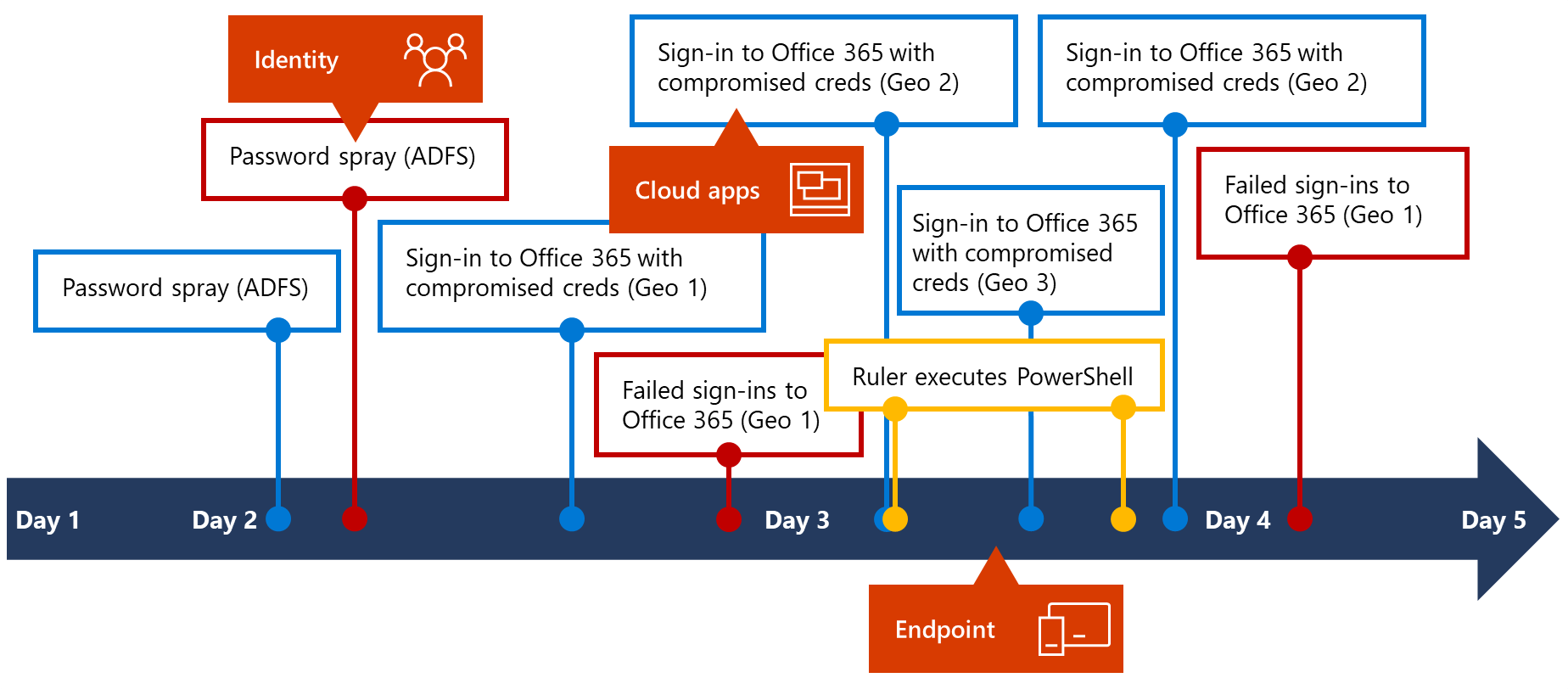
Inside Microsoft 365 Defender: Mapping attack chains from cloud to endpoint | Microsoft Security Blog
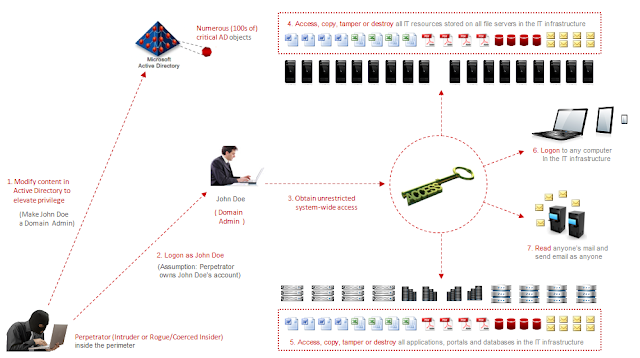
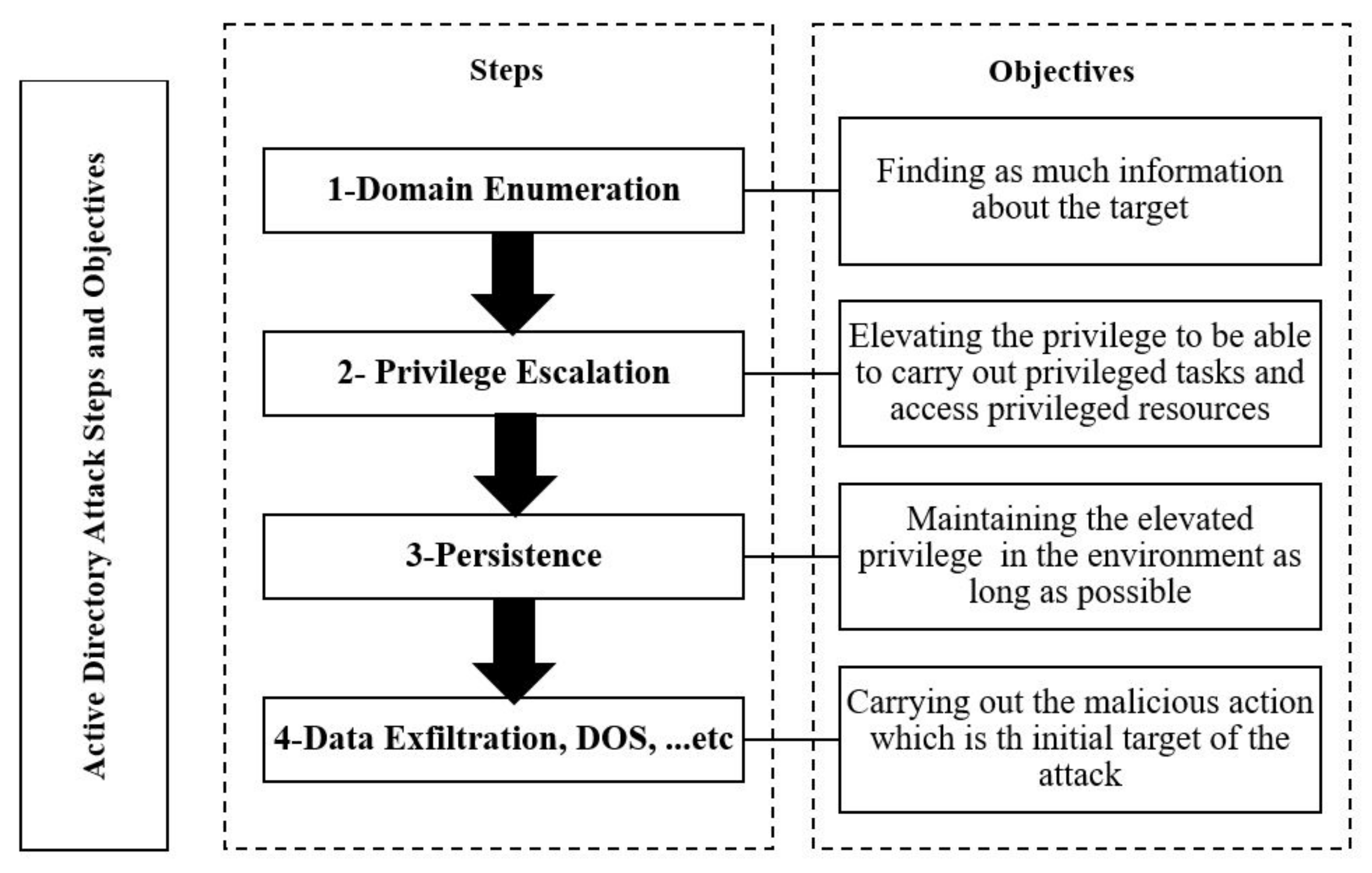
GitHub - infosecn1nja/AD-Attack-Defense: Attack and defend active directory using modern post exploitation adversary tradecraft activity
GitHub - AD-Attacks/Active-Directory-Penetration-Testing: Active Directory Penetration Testing for Red Teams











-1.webp)

